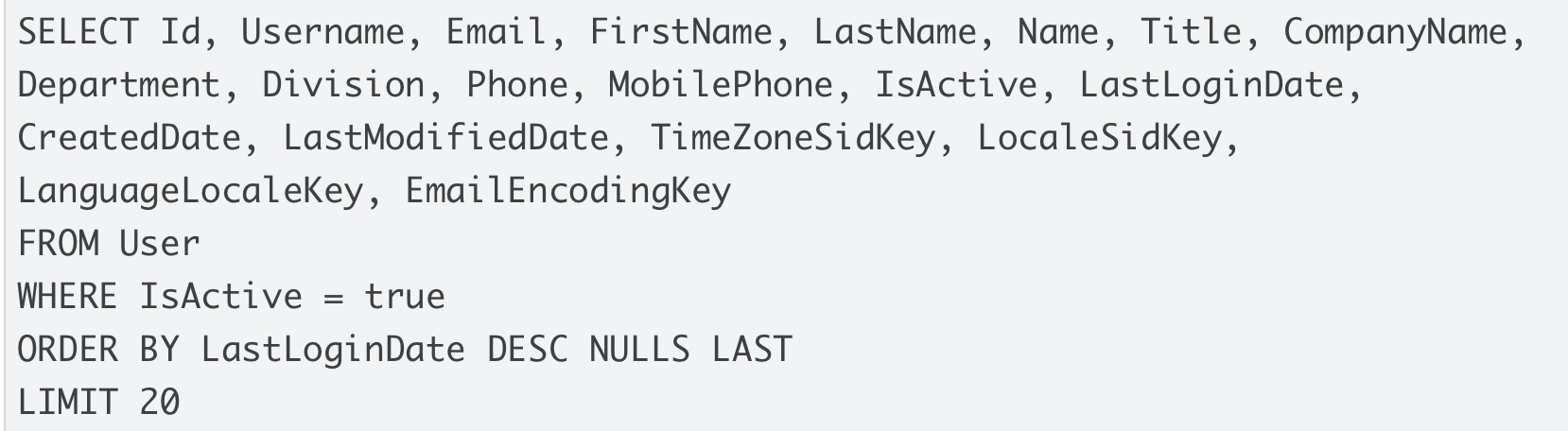
Google Confirms Workspace Accounts Also Hit in Salesforce–Salesloft Drift Data Theft Campaign
Threat Score:
69
20 articles
100.0% similarity
3 days ago
Article Timeline
20 articles
Click to navigate
Related Articles
20 articles
1
Score
Read more
81
100.0% similarity
2
Google Warns Salesloft OAuth Breach Extends Beyond Salesforce, Impacting All Integrations
Score
Read more
69
100.0% similarity
3
Google Confirms Potential Compromise of All Salesloft Drift Customer Authentication Tokens
Score
Read more
65
100.0% similarity
4
Google: Salesloft Drift breach hits all integrations
Score
Read more
64
100.0% similarity
5
Hundreds of Salesforce customers impacted by attack spree linked to third-party AI agent
Score
Read more
60
100.0% similarity
6
Salesloft breached to steal OAuth tokens for Salesforce data-theft attacks
Score
Read more
60
100.0% similarity
7
Hackers Abuse Compromised OAuth Tokens to Access and Steal Salesforce Corporate Data
Score
Read more
54
100.0% similarity
8
Widespread Data Theft Targets Salesforce Instances via Salesloft Drift
Score
Read more
53
96.0% similarity
9
Salesloft OAuth Breach via Drift AI Chat Agent Exposes Salesforce Customer Data
Score
Read more
53
100.0% similarity
10
Salesforce data theft campaign exposes SaaS integration risks
Score
Read more
51
100.0% similarity
11
Salesforce data missing? It might be due to Salesloft breach, Google says
Score
Read more
51
100.0% similarity
12
Salesloft breached to steal OAuth tokens for Salesforce data-theft attacks
Score
Read more
51
96.0% similarity
13
"Widespread data theft" hits Salesforce customers via third party
Score
Read more
50
100.0% similarity
14
Google warns Salesloft breach impacted some Workspace accounts
Score
Read more
50
100.0% similarity
15
Hundreds of Salesforce customer orgs hit in clever attack with potentially huge blast radius
Score
Read more
49
100.0% similarity
16
Salesloft Drift Hacked to Steal OAuth Tokens and Exfiltrate from Salesforce Corporate Instances
Score
Read more
49
100.0% similarity
17
Google Identifies ‘Widespread Data Theft’ Impacting Salesforce-Salesloft Drift Users
Score
Read more
49
100.0% similarity
18
Attackers steal data from Salesforce instances via compromised AI live chat tool
Score
Read more
48
100.0% similarity
19
UNC6395 targets Salesloft in Drift OAuth token theft campaign
Score
Read more
47
100.0% similarity
20
Salesloft Drift compromised en masse, impacting all third-party integrations
Score
Read more
47
100.0% similarity