The jobs
your team actually has.
Six recurring problems CTI teams hit every week, and how ThreatCluster does the heavy lifting on each. Pick the one that's on your plate today and skip to it.
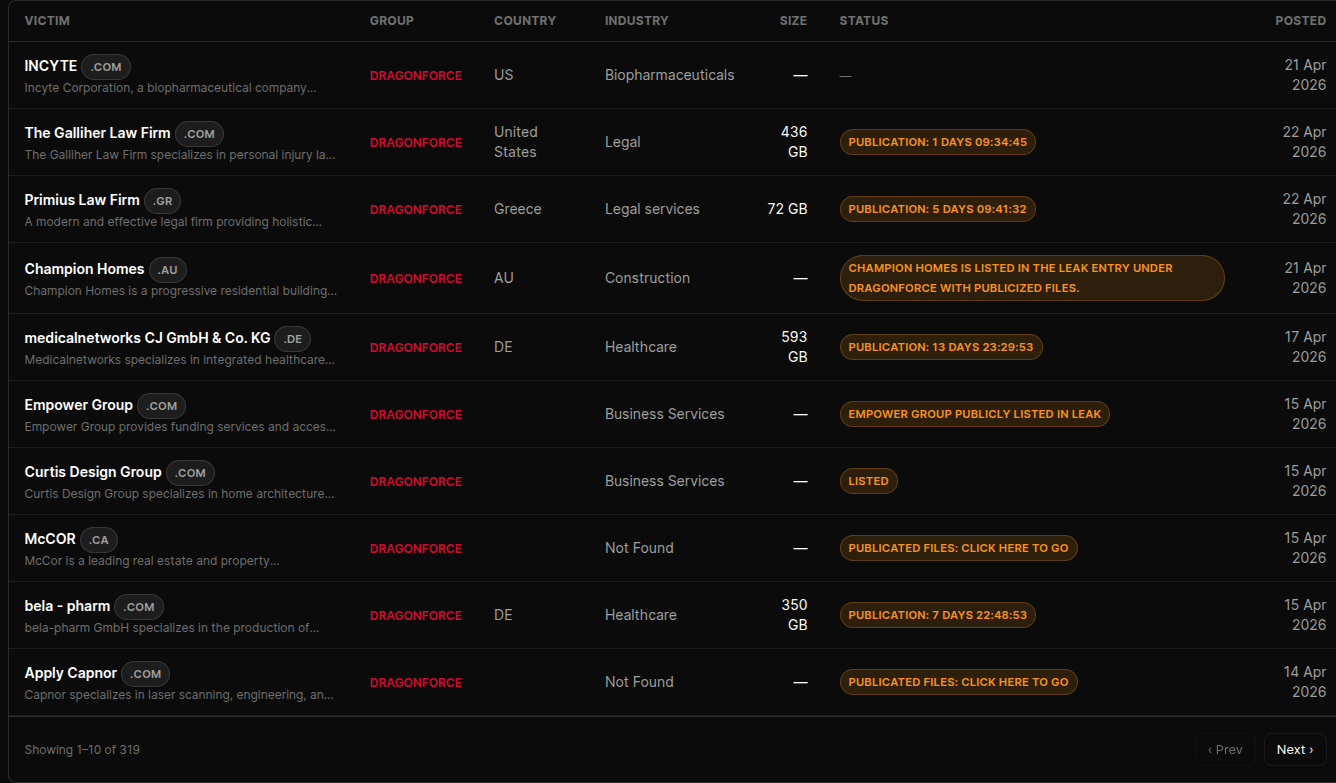
Know when ransomware crews target your clients.
Every active leak site posts new victims daily. The hard part isn't knowing ransomware exists, it is spotting the moment one of your clients, suppliers, or partners is named — often hours before they disclose publicly.
ThreatCluster monitors ransomware leak sites in real time, matches victim postings against your tracked domains and entity list, and pings the right channel the second a match lands.
 click to expand
click to expand
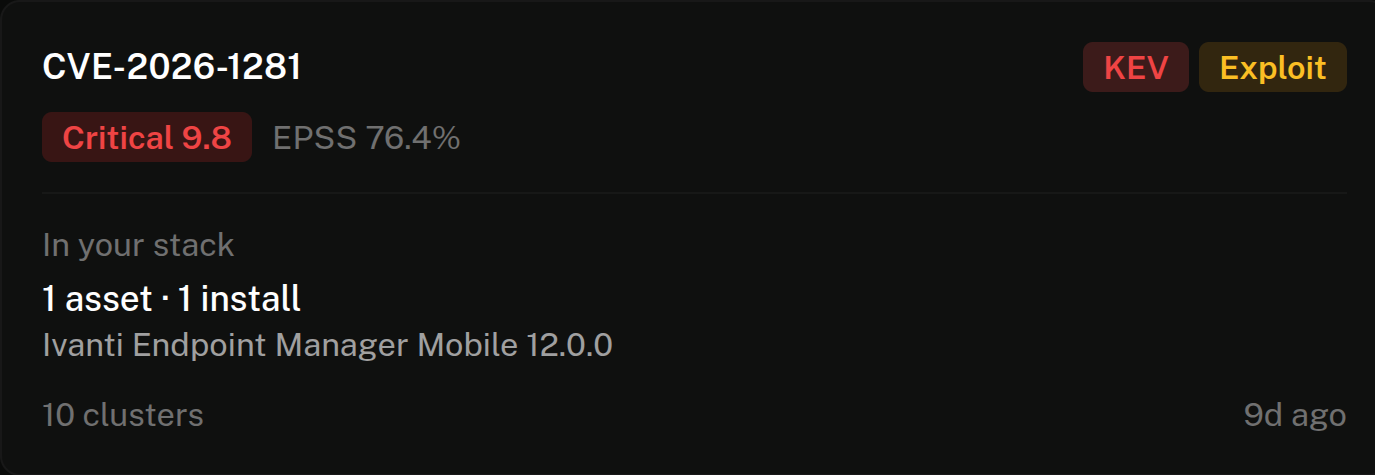
Patch the CVEs that matter, not the CVSS 9s nobody exploits.
A CVSS 9.8 in a product nobody runs is a lower priority than a CVSS 7.2 already in the KEV catalog touching your stack. Most teams know this. Almost none of them have a feed that actually shows them which is which without an afternoon of spreadsheet work.
Pull your asset inventory in, layer KEV / EPSS / public PoC availability over it, and ThreatCluster ranks the queue by what CISA's SSVC framework says you should act on this week.
 click to expand
click to expand
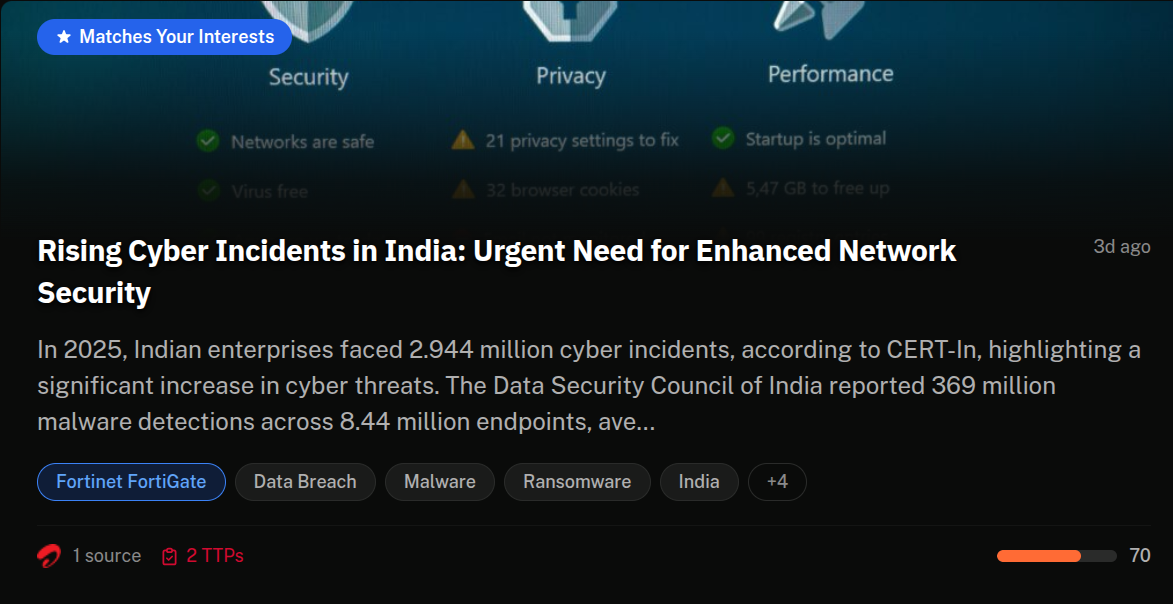
Catch supplier breaches before procurement asks.
Most third-party-risk programs check vendors at onboarding and then again at renewal. The interesting twelve months sit in between. If a key supplier gets popped, you want to know on the day, not the day your CFO sees it in the news.
Pin every supplier domain into a custom feed. When a cluster mentions any of them — breach disclosure, leak-site posting, CVE in their stack, an actor known to target them — you get alerted with the source already in hand.
 click to expand
click to expand
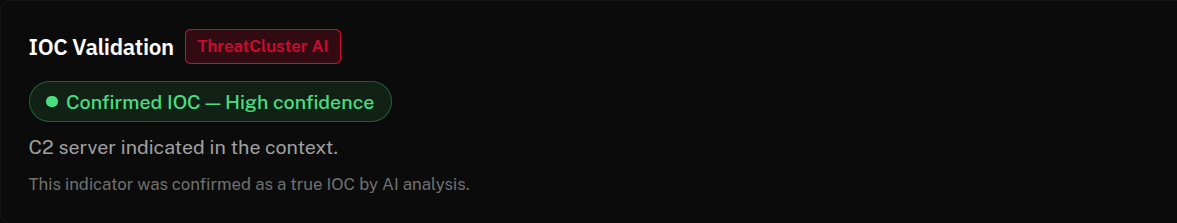
Enrich detections without leaving the SIEM.
A SIEM alert on a suspicious IP, hash or domain is the start of an investigation, not the end of one. Analysts spend most of the next ten minutes pivoting into open tabs to figure out: have we seen this before, who owns it, what malware is it tied to, what's the campaign context?
ThreatCluster pushes that context directly into the SIEM. Webhook a hit into Splunk, Sentinel, Elastic or OpenSearch and the entity intelligence — profile, related entities, latest clusters, MITRE techniques, suggested hunt queries — is attached to the alert.
 click to expand
click to expand
Run a hundred clients without a hundred tabs.
MSSPs aren't running one CTI program. They're running one per client, each with its own assets, suppliers and threat picture. Doing that in a tool built for a single tenant means either everything bleeds together or analysts spend the morning switching browser profiles.
ThreatCluster is multi-tenant from the database up. One feed per client. White-labelled briefings per client. Alert routing per client. Per-customer scoping built in — the right team sees the right intelligence, the wrong team never does.
 click to expand
click to expand
Brief the board in a paragraph, not a deck.
Most executive briefings on cyber are six slides too long. Leadership wants the answer to two questions: are we more exposed than last week?, and what should we be doing about it?
Wire a custom feed to the threats that matter to your business, schedule a weekly report on it, and ThreatCluster writes the briefing live from the week's clusters — entity activity, top incidents, supplier exposure, ransomware posture — with inline citations so every claim is traceable.
 click to expand
click to expand
None of these your job? Tell us yours.
Most CTI work fits the patterns above, but the platform flexes a long way past them. Tell us what your week looks like and we'll show you the surfaces that match.