Threat intelligence,
pointed at your boxes.
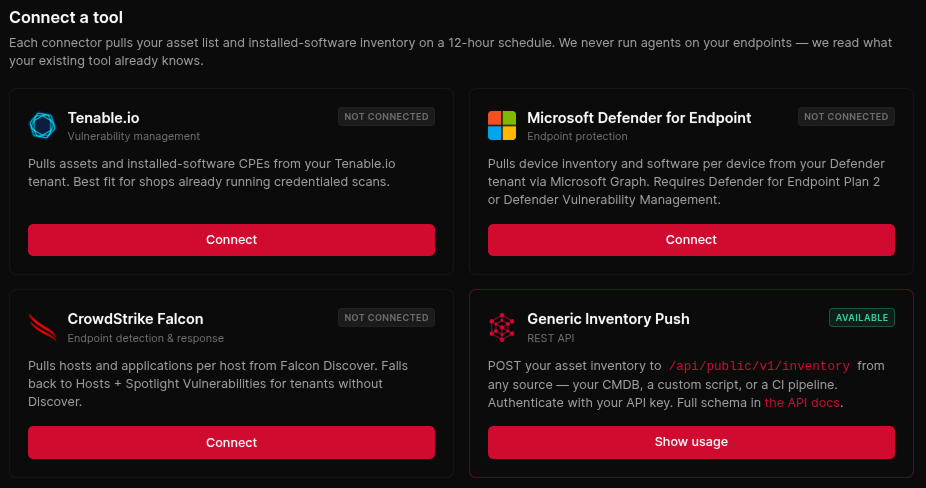
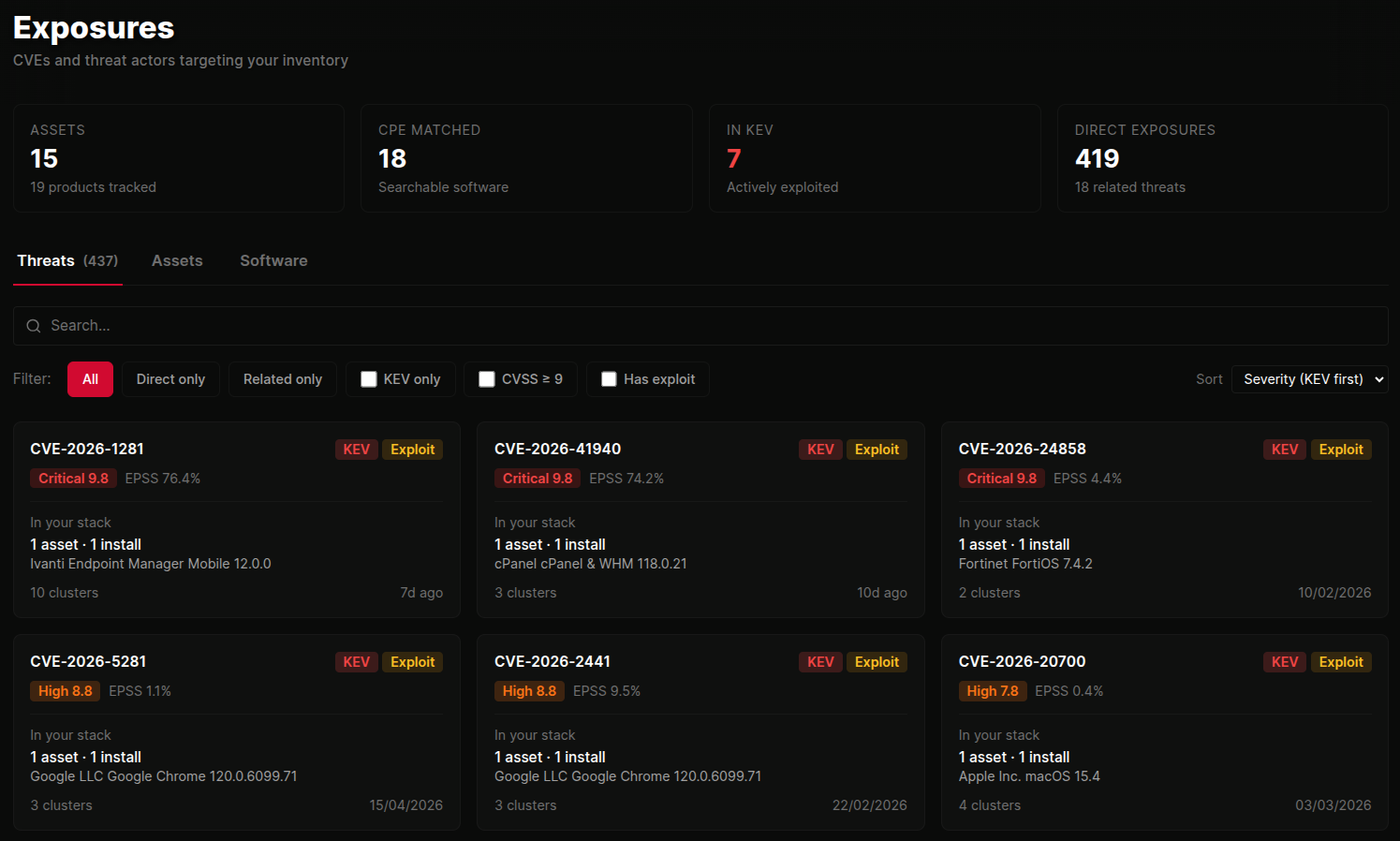
A CVE feed is generic. ThreatCluster Exposures pairs the live threat graph with each customer's actual inventory and tells you, host by host, what to patch first.
Two streams against your stack.
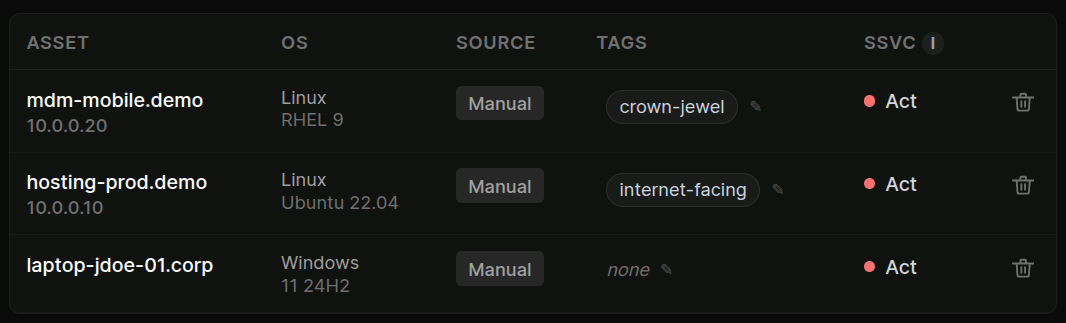
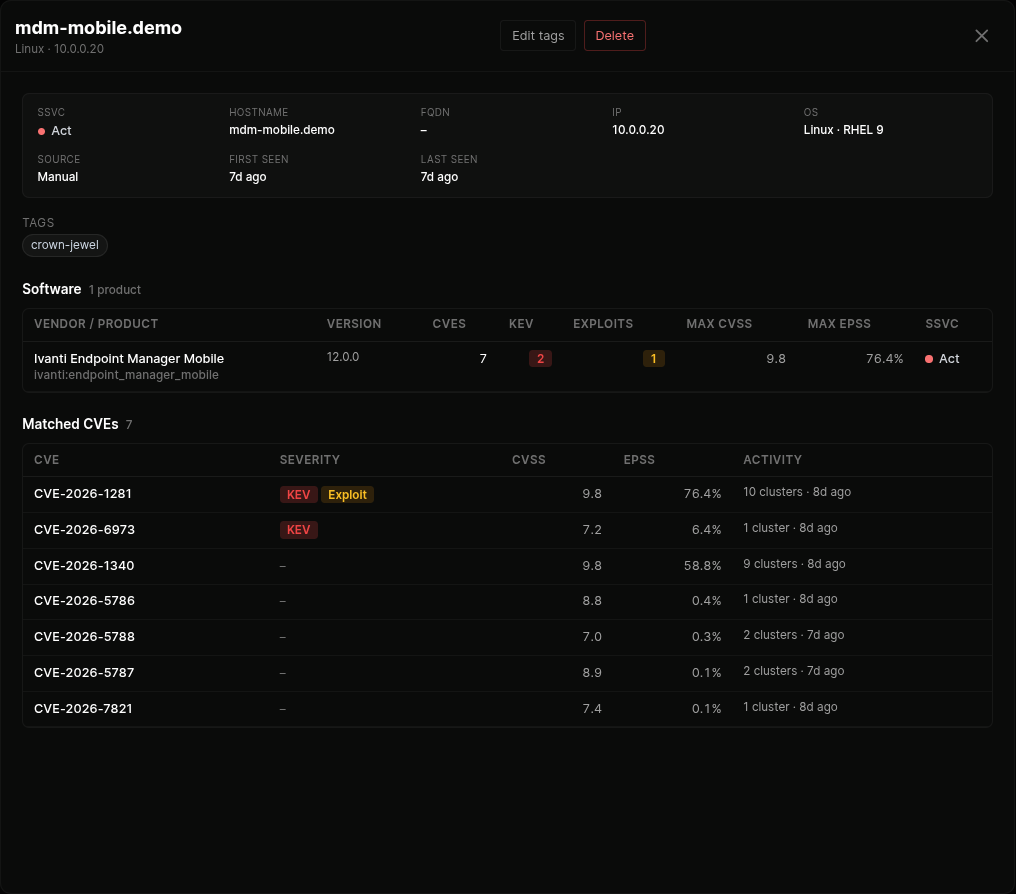
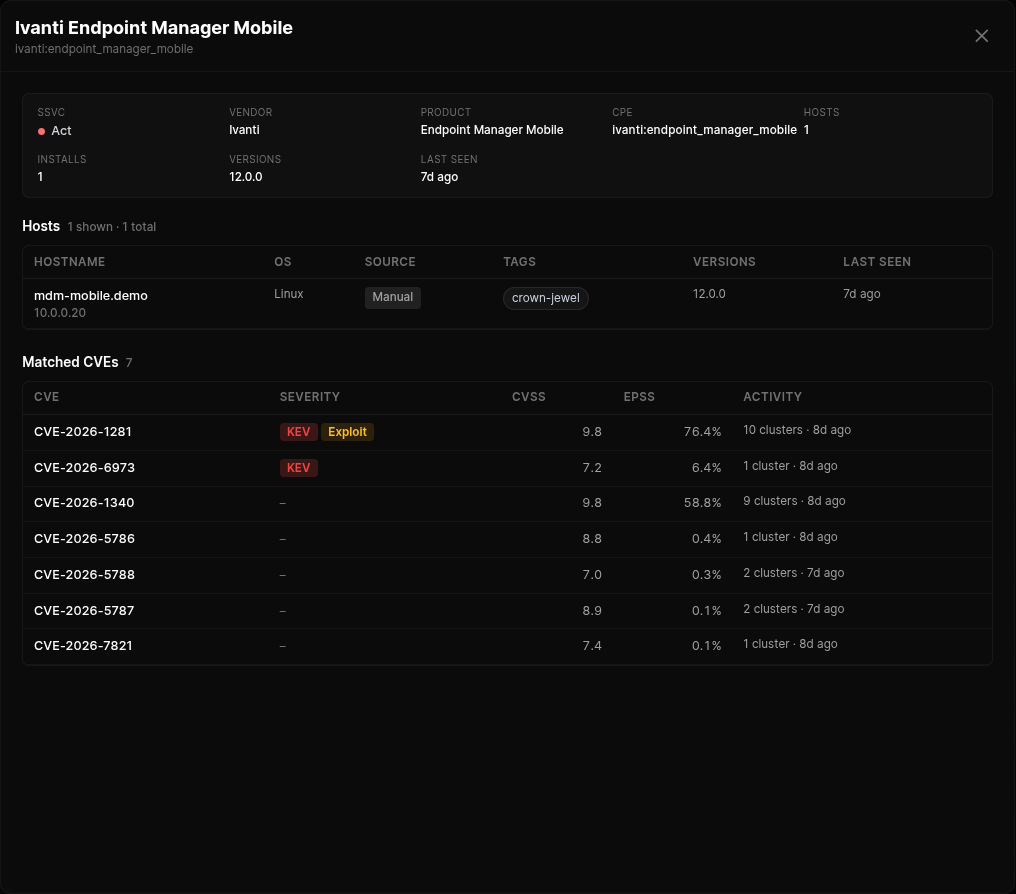
Exposures joins the live threat feed with each client's asset inventory and tells you what to patch first. Two overlays: direct exposures (CVEs against their installed software) and related threats (actors and malware targeting their tech).
Filter by KEV-only, CVSS ≥ 9, or has-exploit. Sort by severity, latest activity, asset reach, or cluster volume. Search by CVE, product, or vendor to jump straight in.
- Direct CVE matches against installed software
- Related threat actors and campaigns targeting their stack
- Per-asset breakdown showing which boxes are affected
- Filter by KEV, EPSS threshold, public-exploit availability
 click to expand
click to expand
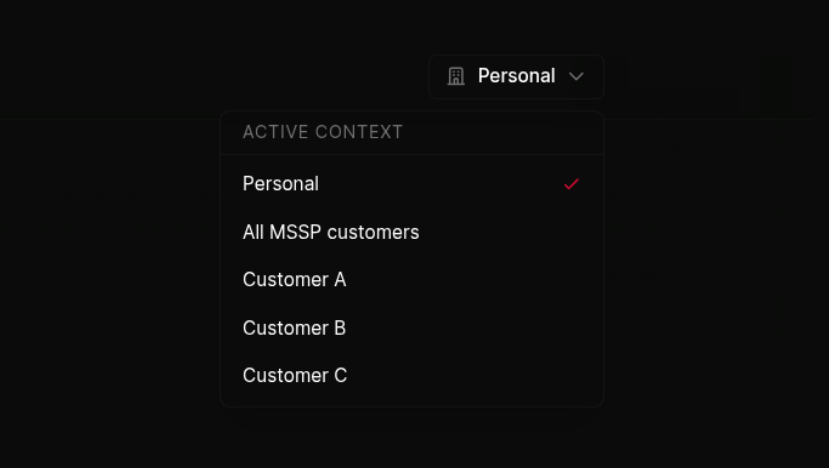
Per-customer, end to end.
For MSSPs, every asset, every CVE match, every SSVC ranking is scoped to a specific customer. Switch the active customer from the navbar and the entire exposures page re-scopes. Assets, software, threats, all of it.
Each customer's data stays in its own lane. Analysts see only what they're allowed to see, and the switcher makes it impossible to accidentally take action against the wrong client.
 click to expand
click to expand