Our collection.
Not someone else's.
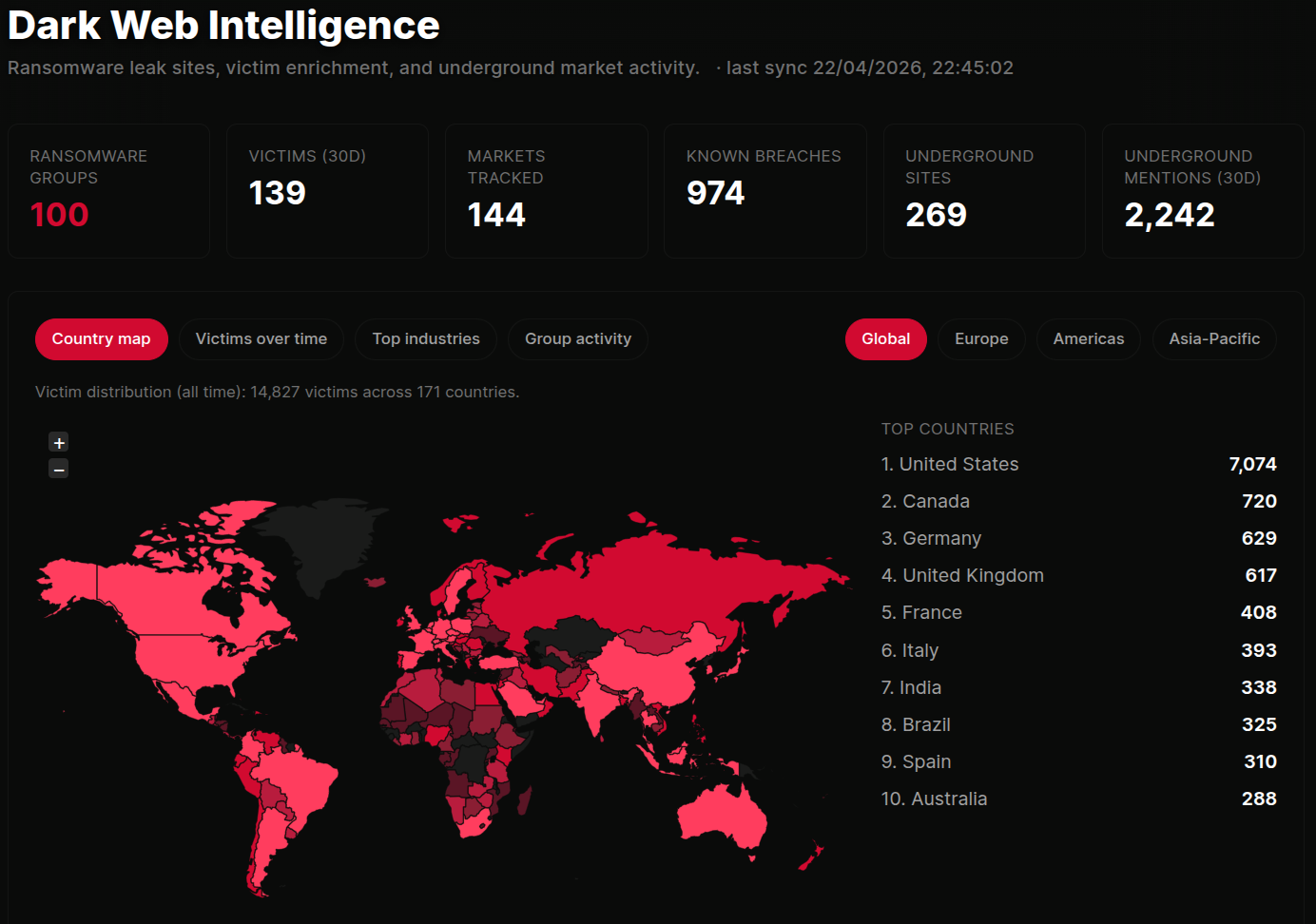
Most dark web tools resell the same handful of upstream feeds. ThreatCluster runs its own collection stack across ransomware leak sites, underground forums, and Tor markets. We discover, enrich, and surface the content directly.
Three independent scrapers.
One scraper covers ransomware and data-leak group sites. The second covers underground forums. That includes paste sites, initial-access broker boards, combolists, and defacement archives. The third covers Tor and clearnet marketplaces.
Running them independently means a Tor outage on the marketplace side doesn't blind us to leak-site updates, and a forum being seized doesn't take down the ransomware tracking.
 click to expand
click to expand
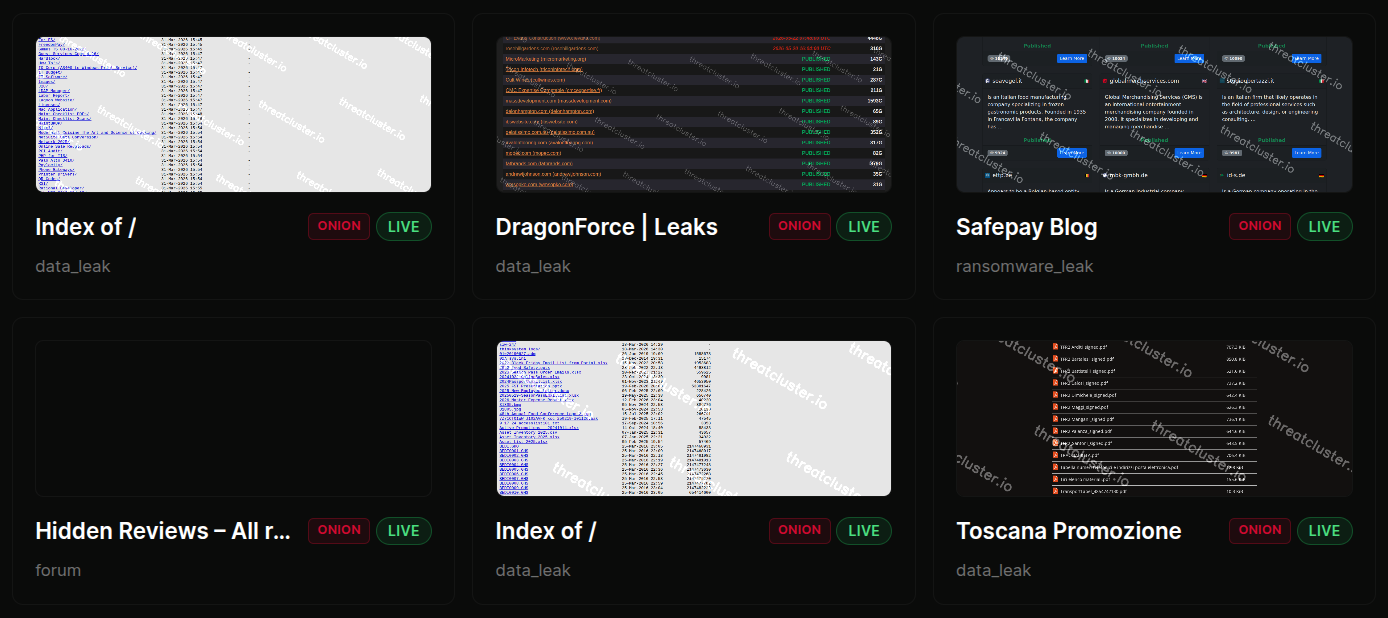
We find our own sites.
Four sources find new sites in parallel. Curated CTI repositories, Tor search engines, GitHub-published onion lists, and Telegram channels.
New candidates go through liveness probing, a depth-1 link harvest, and automated classification. Most competitors buy a list. We build ours.
- Curated CTI repositories
- Tor search engines
- GitHub-published onion lists
- Telegram channels
 click to expand
click to expand
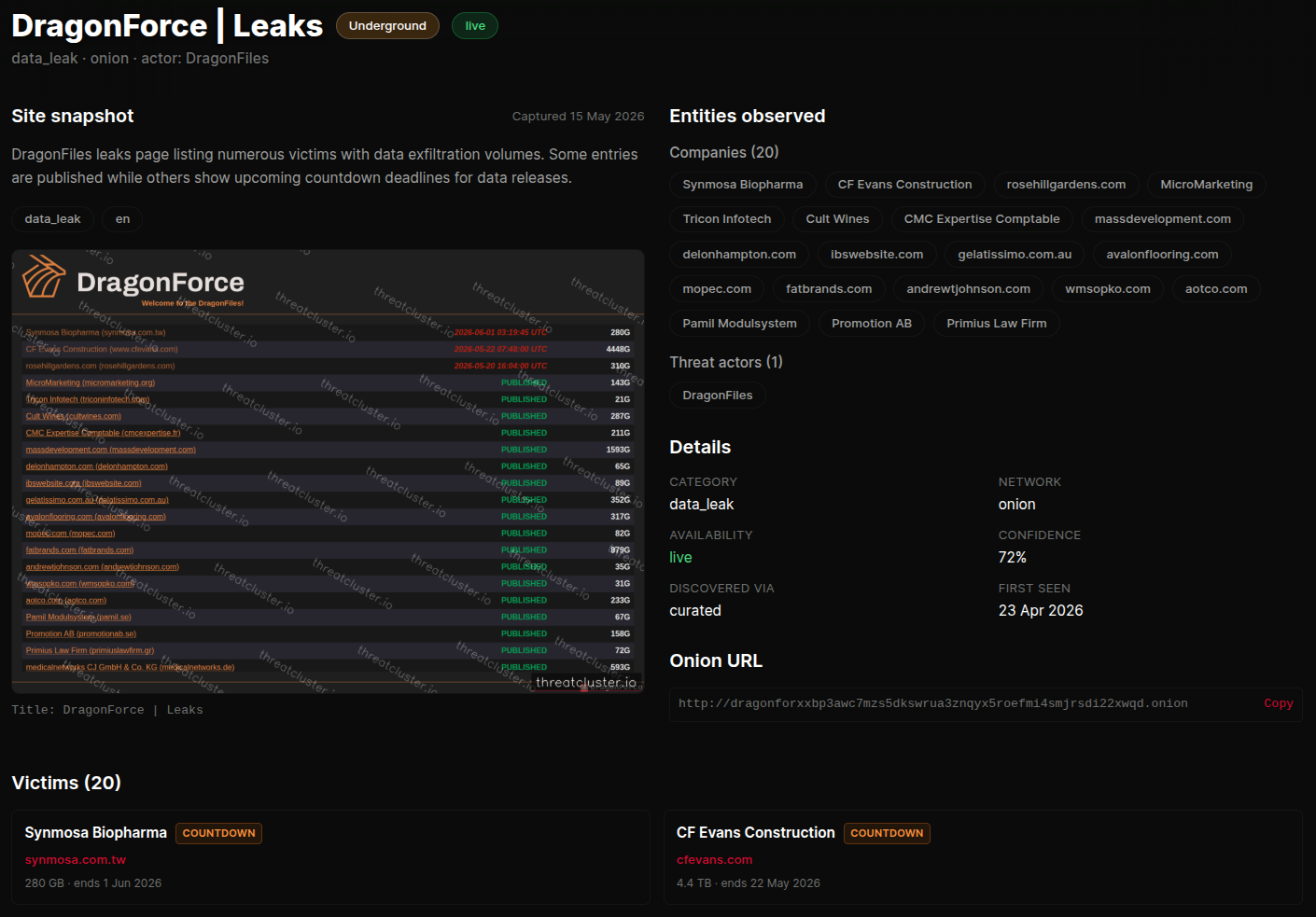
Every page, enriched twice.
We pull out the unambiguous indicators first. Crypto wallets, emails, Tox IDs, XMPP and Telegram handles, PGP blocks, CVE references. Anything with a predictable shape gets captured with a script, not a model.
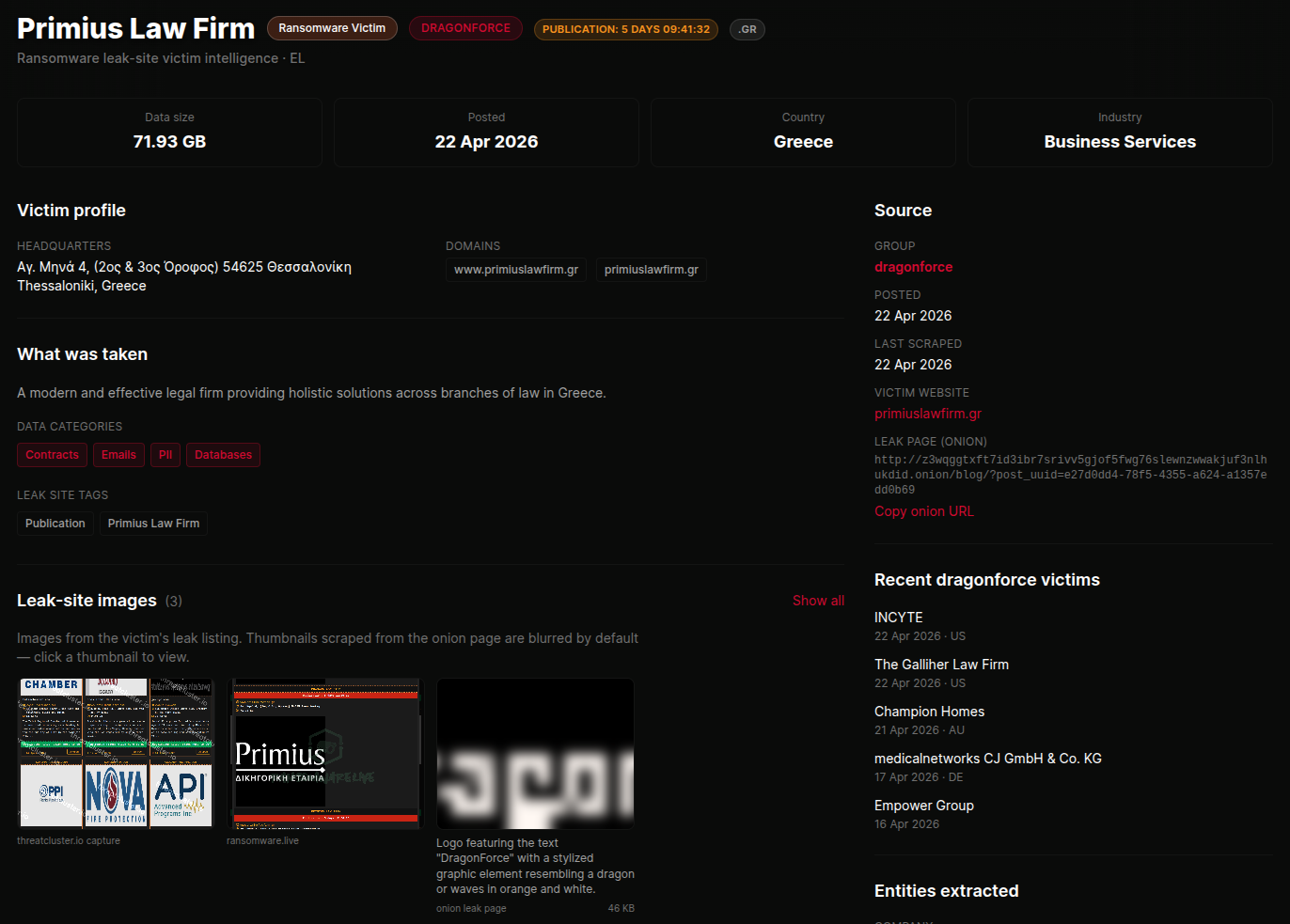
AI then handles the contextual layer. Victim names, tools, attribution, language, and a one-paragraph summary. Everything cross-references into the main entity graph, so a victim domain or a tool name surfaces on its own entity page alongside the news.
 click to expand
click to expand
Surfaced the way an analyst reads it.
Group profile pages with active campaigns and historical victims. Per-victim detail pages with the enriched data attached. Markets with category tags. Underground forum posts with screenshots, captions, and metadata. Breach indexes filterable by country, sector, group, status, or freshness.
 click to expand
click to expand
Alerts when a client's domain hits a list.
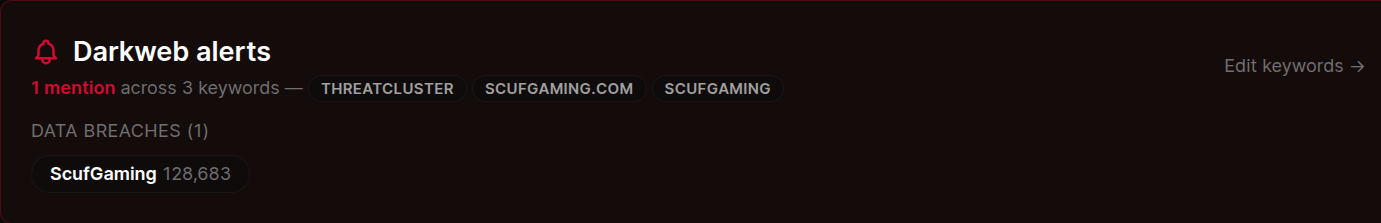
Set the domains and supplier names you care about. When they appear in a ransomware victim post, a forum drop, a combolist, or a market listing, an alert fires through the same webhook and digest channels that the rest of the platform uses.
For MSSPs, alerts route per customer. Each client's mentions stay in their own channel, so the right team gets notified without one client ever seeing another client's hits.
 click to expand
click to expand
More of the platform
Watch the leak sites,
not the news cycle.
Live coverage of the leak sites, forums, and markets that matter, with alerts when your clients show up. No reseller, no curation lag.