Indicators that
go where you need them.
Every article that enters the pipeline is extracted for IOCs, validated for confidence, and made available wherever your analysts and tooling need them. STIX, MISP, REST, RSS, CLI.
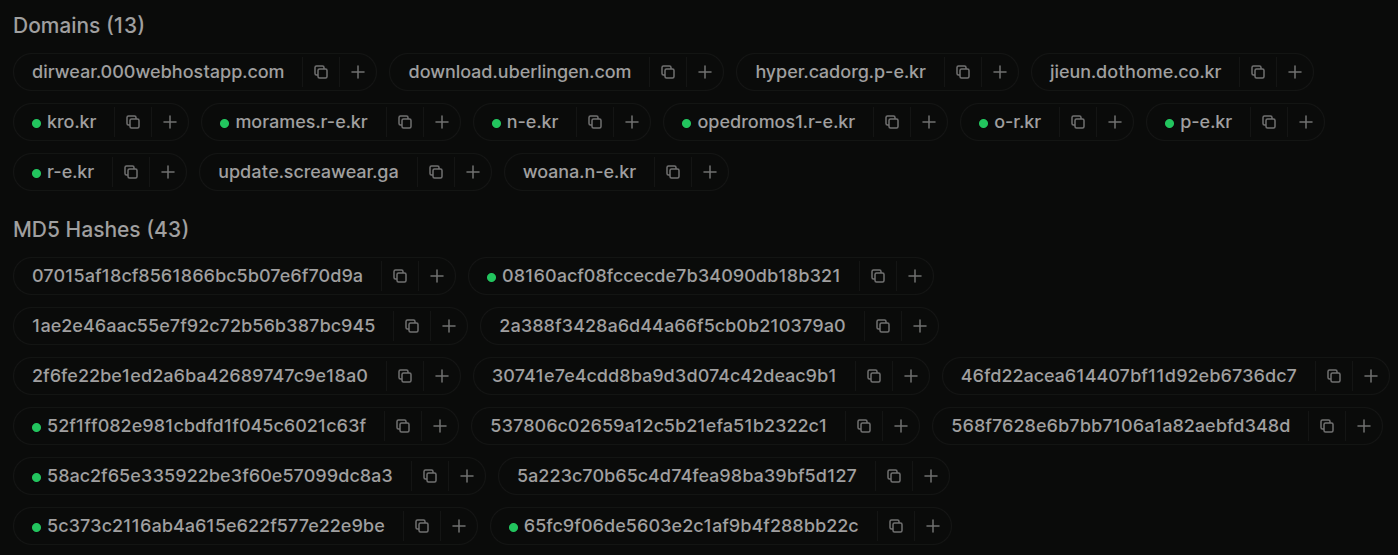
Every article, extracted twice.
The unambiguous indicators come out first. IPs, domains, URLs, hashes, CVE IDs, crypto wallets. Anything with a predictable shape gets captured with a script, not a model.
AI then handles the contextual layer. Threat actors, malware families, MITRE techniques, tools, industries, and targets. Benign domains, invalid hashes, and known false positives are filtered out up front, so the validation queue stays clean.
 click to expand
click to expand
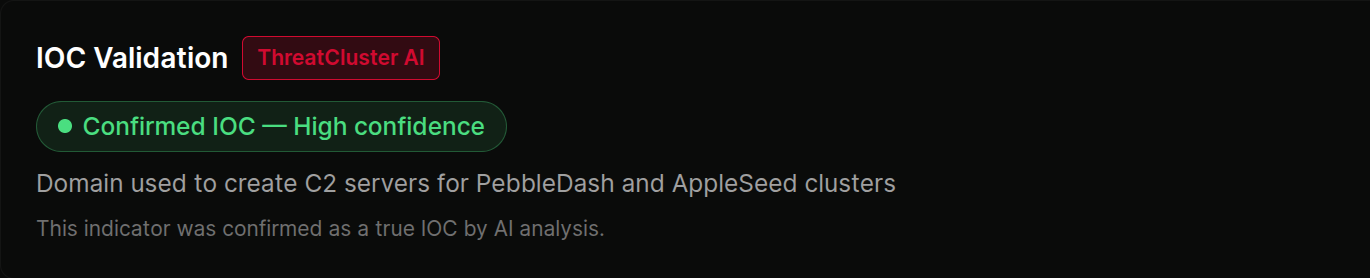
Confidence on every indicator.
Every IOC is assigned a confidence level. High, medium, low, or false positive. Each carries a written justification so analysts know why the model graded it that way.
Confidence feeds every downstream filter, so analysts only see what's been verified. Pending IOCs surface separately for the analyst on triage duty, with an X-IOC-Pending-Count header on every API response so SIEM ingestion can see the validation lag in flight.
 click to expand
click to expand
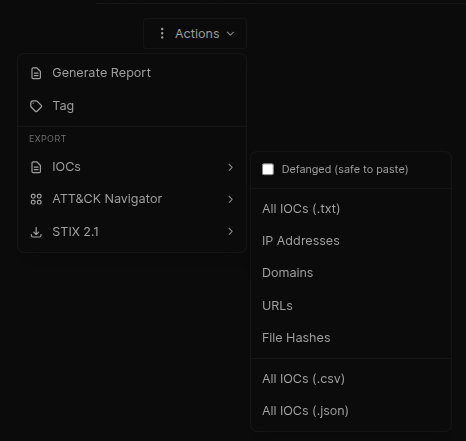
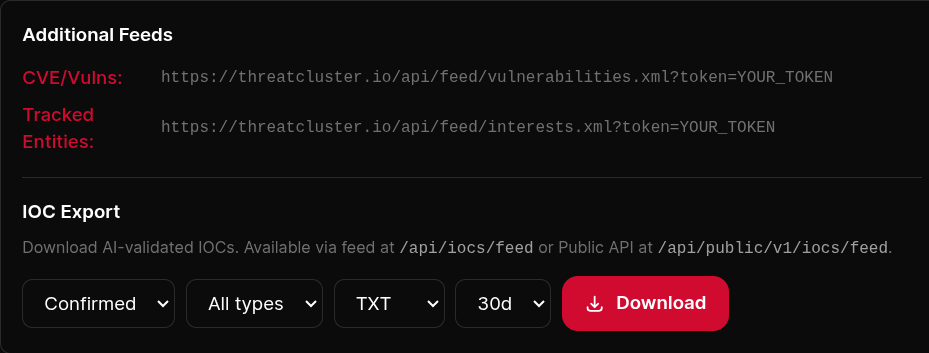
Per-cluster or in bulk.
One cluster's IOCs as TXT for a firewall blocklist, CSV for a spreadsheet, JSON for a script, or STIX 2.1 with TLP marking for a TIP. Or query in bulk by type, confidence, and time window.
Defang on or off per request. ATT&CK Navigator layer for the techniques in the cluster. The full format matrix with auth, tier, and confidence defaults sits at /formats.
 click to expand
click to expand
Native MISP feed.
ThreatCluster ships a native MISP-compatible feed with manifest, hashes index, and event JSON. UUIDs are stable across regenerations, so MISP correlation works cleanly and event re-pulls don't generate duplicate records.
Authenticated tier carries 50 events with historical replay via ?since= and ?days=. Public tier carries 10 recent events. MISP Galaxy clusters auto-attach for recognised threat actors and ransomware groups.
 click to expand
click to expand
Into your SIEM, however you ingest.
REST API for direct pulls. RSS for feed-based ingestion. Webhook push into Splunk, Microsoft Sentinel, Elastic, or OpenSearch. Filter by confidence, type, and freshness on the wire so you don't have to filter post-ingest.
Hunting queries for the same IOCs export natively in KQL, SPL, and Lucene from the Hunt page.
 click to expand
click to expand
More of the platform
Pipe the IOCs
where they need to go.
Eleven consumption surfaces, one entity graph behind them. STIX for your TIP, MISP for your sharing community, REST for your scripts, RSS for your dashboard.