Click any entity.
Get the full picture.
Every threat actor, malware family, tool, CVE, vendor, and technique mentioned anywhere on the platform has its own intelligence page. Built from the platform's own data, not a static reference book.
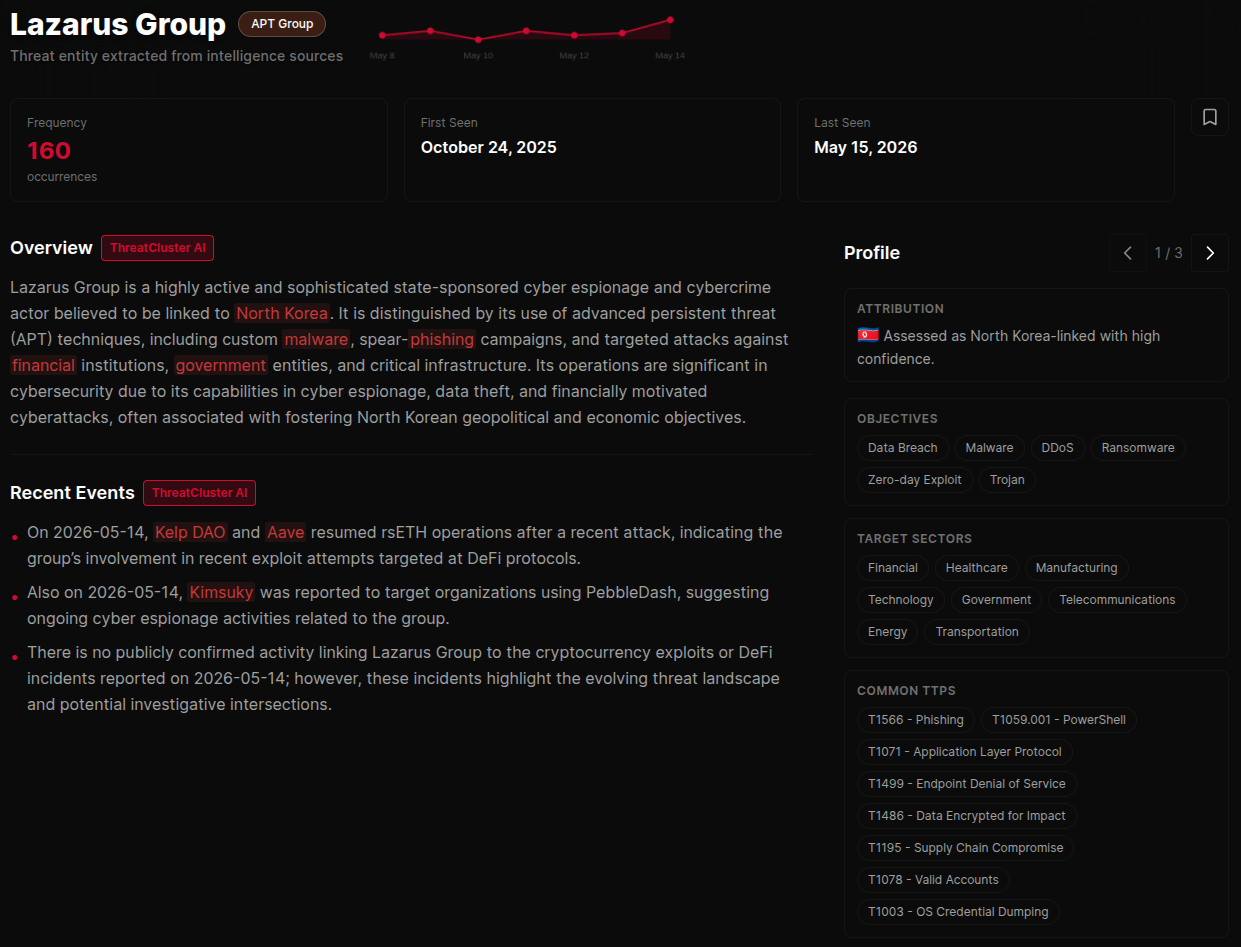
The full intelligence page.
AI-generated overview, recent events, threat profile, and frequency tracking from first seen to last seen. Drawn from the intelligence the platform has collected on this entity, not from a third-party threat database.
The threat profile covers capabilities, delivery methods, targeted platforms, target regions, target sectors, common TTPs, associated campaigns, and associated CVEs. Every section is derived from co-occurrence in the cluster data.
 click to expand
click to expand
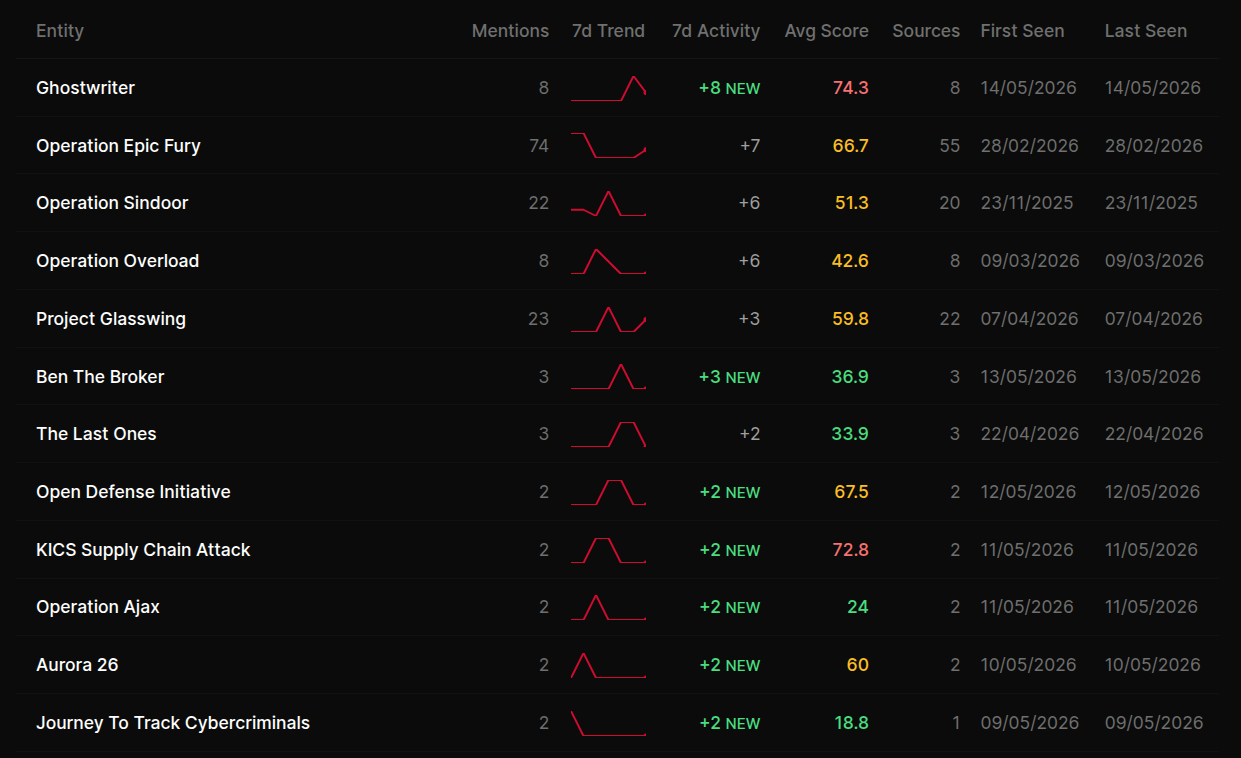
Living, not static.
Every entity profile updates as new clusters land. New campaign mentioning this APT? It surfaces in the recent events block within minutes. New malware family observed in the same campaigns? It appears in the relationship graph on the next render.
Frequency charts plot mentions over time so you can see when an entity went quiet, when it returned, and when its activity spiked.
 click to expand
click to expand
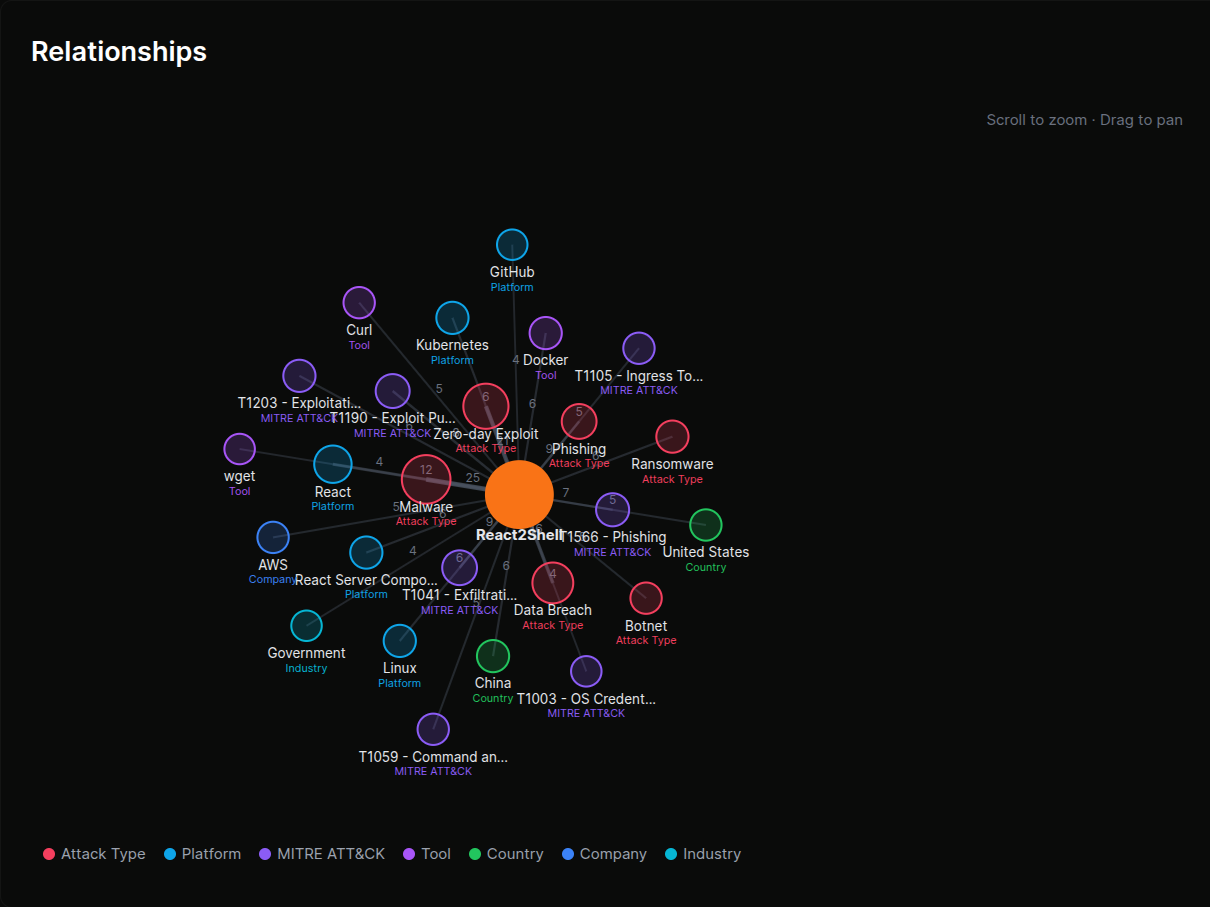
Relationship graph.
Every entity page maps its connections to other entities visually. Which threat actors use which malware. Which malware targets which platforms. Which CVEs are associated with which campaigns.
Explore laterally across the graph to find connections that aren't obvious from reading individual clusters. A tool used by three unrelated APTs is a story; a malware family targeting the same six platforms across a year is a pattern.
 click to expand
click to expand
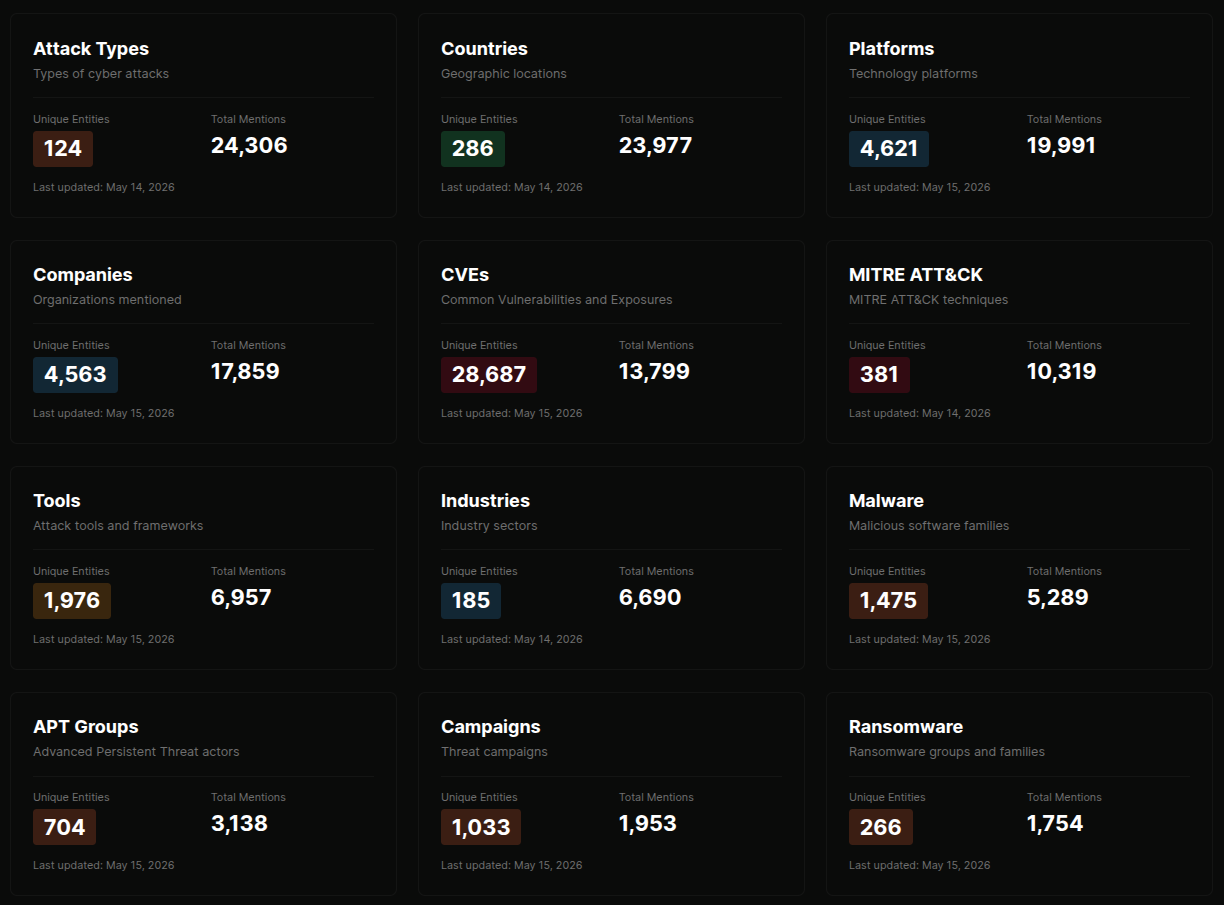
Searchable, browseable, exportable.
Search by name across every entity type. Browse by category, by frequency, or by recent activity. Export individual entity profiles as JSON, or pull the underlying relationship data via the REST API for downstream graph analysis.
For IOC-type entities (IPs, domains, hashes, emails, crypto wallets), the entity page also surfaces the AI confidence verdict and the underlying reason. See IOCs and Exports for the validation pipeline.
 click to expand
click to expand
More of the platform
Every entity. Every connection.
One page.
Drawn from the intelligence the platform has collected, not copied from a third-party reference book. Updates as the situation does.