Your feed.
Hyper specific.
Describe the feed in plain English. Attach the entities, sectors, and assets that matter to you. Get the only clusters you actually want to see, in a feed that's yours.
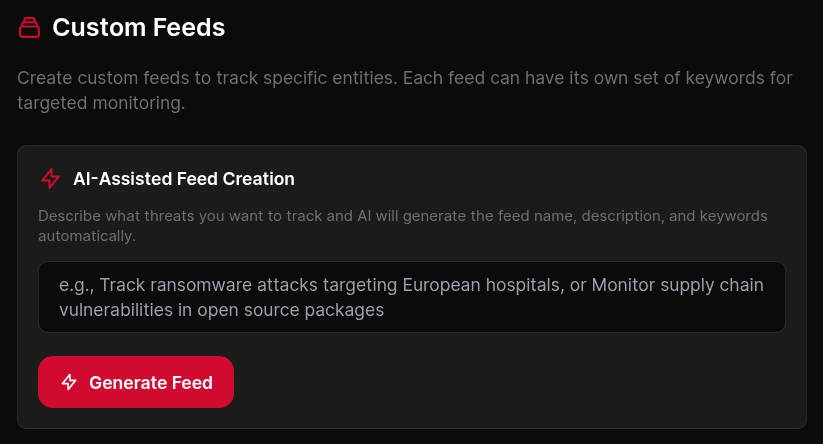
Tell us what you care about.
Start with one sentence. "Ransomware activity against UK manufacturing." "CVEs in the products my top ten clients run." "Anything mentioning Scattered Spider, ALPHV, or their tooling."
AI translates that into a structured filter against the live entity graph. You see what got picked up, adjust if it missed something, and save. The whole loop is plain English in, working feed out.
 click to expand
click to expand
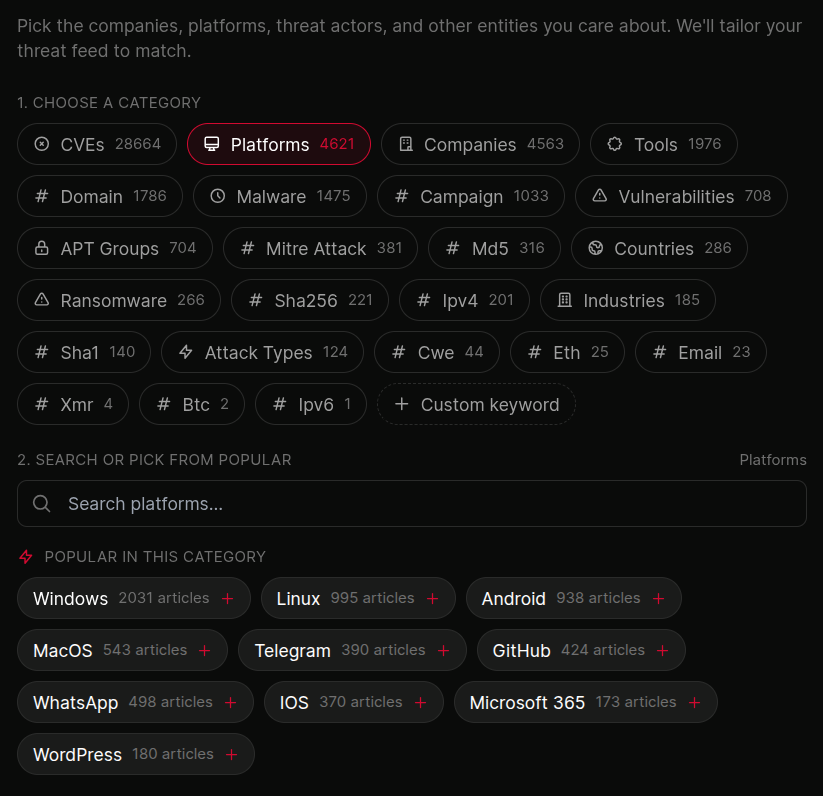
Attach the entities you actually track.
Pin threat actors, malware families, vendors, products, CVEs, sectors, regions, or your own assets. The feed only fires on clusters that touch those entities, so you stop reading anything that isn't yours to read.
Mix and match entity types in one feed. A "client X exposure" feed might pin three vendors, two CVEs, and the actor groups known to exploit them. One feed, one tab, one story.
 click to expand
click to expand
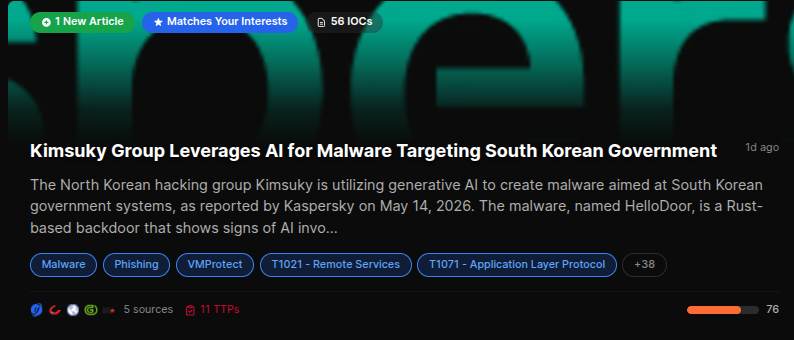
This is the actionable bit.
A global threat feed is interesting. A feed that only surfaces what affects your environment is actionable. The same cluster that's noise to everyone else is the one your client needs to know about today.
Custom feeds turn the platform from a reading list into a working surface. One per client, one per sector, one per investigation. Switch between them from the sidebar.
 click to expand
click to expand
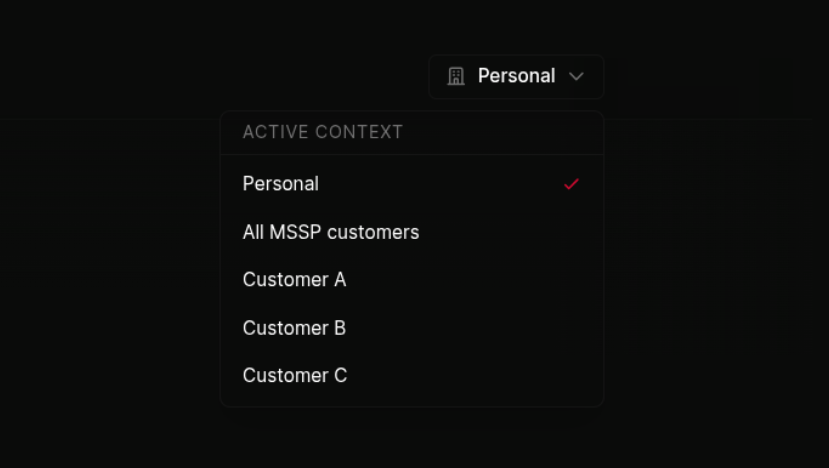
Built for MSSPs.
One feed per client. Each feed scoped to that client's asset list, vendors, and exposures. The analyst on the morning shift opens "Client A" and sees only Client A's world.
Feeds attach to the same per-customer scoping the rest of the platform uses, so workflows fired from a feed only ever route to that client's destinations. The right team gets the right alert, and nobody sees what they shouldn't.
 click to expand
click to expand
More of the platform
One feed per client.
Built in a sentence.
Describe what you want to see. Pin the entities. Get the actionable, hyper-specific feed your team will actually open every morning.